A simulated phishing exercise is a cybersecurity training method used to test and educate employees about phishing threats. Hacking for Good can send fake but realistic phishing emails to organizational staff to see how they respond-whether they click on suspicious links, enter sensitive information, or report the email as suspicious, all in a safe and controlled environment. The goal isn’t to trick or punish employees, but to raise awareness and improve their ability to recognize and avoid real phishing attacks. Phishing is one of THE MOST common ways cybercriminals gain access to networks, often leading to data breaches, financial loss, or system compromise. By running simulations, companies can identify weak spots in their defenses, provide targeted training, and build a culture of caution and vigilance. These exercises also help IT teams measure the effectiveness of their security awareness programs and reduce the overall risk of a successful attack.
Related Post
Online Footprint Review
An online footprint evaluation for a nonprofit is a cybersecurity-focused review of how much information the organization—and its staff, volunteers, and donors—are exposing publicly on the internet. This includes analyzing the nonprofit’s website, social media accounts, staff directories, event listings, and any other digital content that could reveal sensitive or exploitable details. While transparency is […]
Network Traffic Inspection
Network traffic inspection is the process of monitoring and analyzing the data that flows in and out of a nonprofit’s computer network. This includes emails, web activity, file transfers, and other communications between devices and external servers. For nonprofits, inspecting network traffic is a vital cybersecurity measure that helps detect suspicious behavior, prevent data breaches, […]
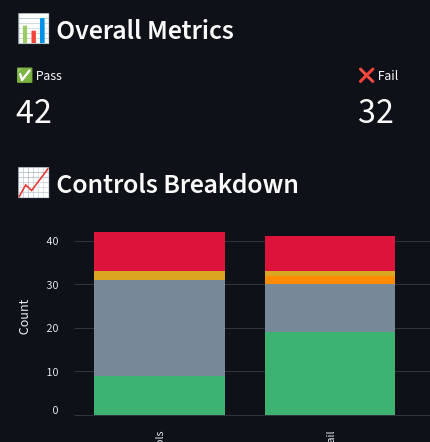
A Google Workspace security audit provides a structured, in‑depth review of how an organization’s environment is configured, governed, and monitored. The process evaluates administrative settings, identity and access controls, data‑handling policies, and collaboration configurations to identify gaps that could expose sensitive information or weaken organizational resilience. The assessment is anchored in the CIS Benchmarks for […]