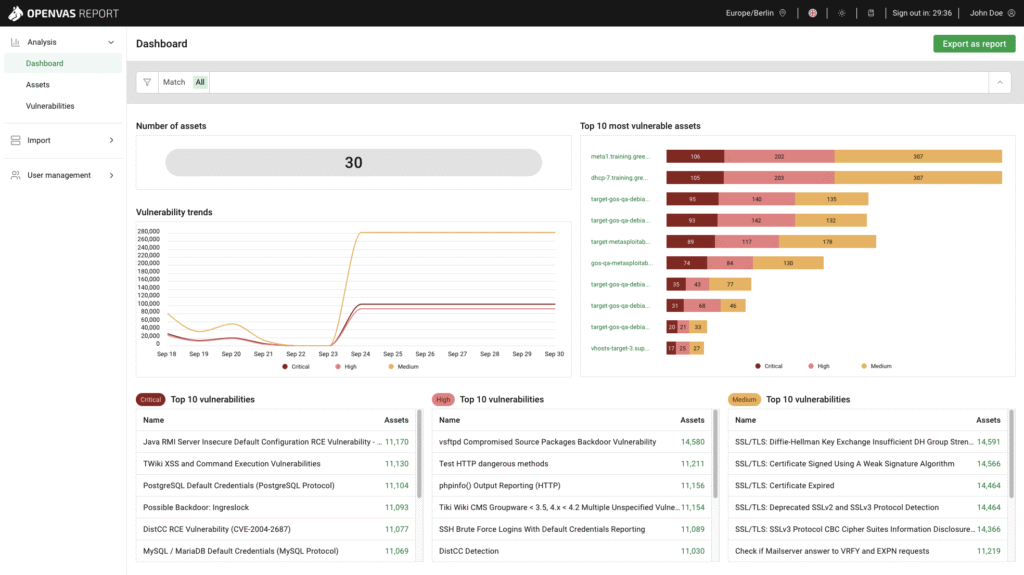
Network scanning is one of the first and most important steps in protecting a computer network from cyber threats. It’s the process of examining a network to discover all connected devices, open ports, and running services—essentially creating a map of everything that’s online. For IT administrators, this is a vital tool that helps them understand what’s on their network, how it’s configured, and where vulnerabilities might exist. Hacking for Good uses network scans to identify outdated software, misconfigured systems, or unauthorized devices that could be exploited by hackers. In short, network scanning gives IT admins the visibility and control they need to keep their systems secure, efficient, and resilient against evolving cyber threats. Not familiar? No problem! Hacking for Good provides a custom appliance to conduct the scans- simply plug it in to your network, power it on, and walk away!
Related Post
The Cybersecurity Maturity Model Certification (CMMC) framework is a set of cybersecurity standards developed by the U.S. Department of Defense (DoD) to ensure that contractors and subcontractors properly protect sensitive government informationOrganizations working with the federal government are required to meet specific CMMC levels based on the nature of their work, making it an essential […]
Simulated Phishing Exercises
A simulated phishing exercise is a cybersecurity training method used to test and educate employees about phishing threats. Hacking for Good can send fake but realistic phishing emails to organizational staff to see how they respond-whether they click on suspicious links, enter sensitive information, or report the email as suspicious, all in a safe and […]
Online Footprint Review
An online footprint evaluation for a nonprofit is a cybersecurity-focused review of how much information the organization—and its staff, volunteers, and donors—are exposing publicly on the internet. This includes analyzing the nonprofit’s website, social media accounts, staff directories, event listings, and any other digital content that could reveal sensitive or exploitable details. While transparency is […]